Best practices
Password blacklist
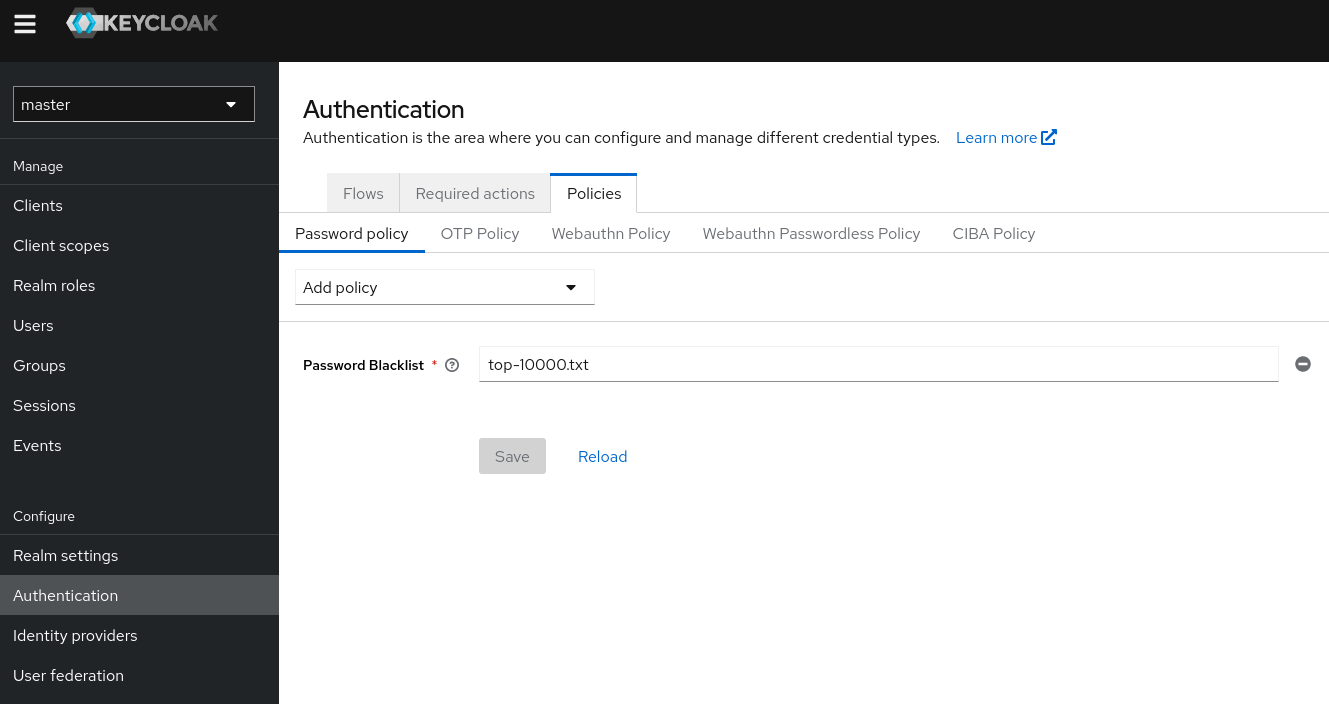
User password must be strong to ensure they can not easily found.
But as user might not realize the weakness of their password, a good practice is to define a password policy. This is a set of rule that a password much conform with.
You might also want to forbid the use of well-known password. This is defined through a Password blacklist, more information on how to configure this feature here.
Brute force detection
Brute force attacks can be used try multiple passwords for a user. The idea is to guess a user’s password by chance.
Keycloak has brute force detection capabilities and can temporarily disable a user account if the number of login failures exceeds a specified threshold.
This should be configured in the Realm settings > Security defenses > Brute force detection

However, this will not prevent your Keycloak from being flooded with attacks based on leaked user / password. This type of attack try to get a session with thousands of login / password pairs on the cluster.
This is based on the fact that user might reuse their password on multiple services.
Brute force detection won't help against that because each try uses a different username which cannot be spotted by Keycloak.
However, Cloud-IAM offers mitigation of this kind of attacks via active filtering of the user requests.
Enforce your Admin Account security
To enhance the security of your Keycloak deployment, we strongly recommend following these best practices when setting up your admin password:
1. Length Matters:
Ensure your password is at least 12 characters long. Longer passwords provide better security again brute force attacks.
2. Randomness is Key:
Create a password that is random and does not resemble common words or proper names. This helps prevent easy-to-guess passwords.
3. Uniqueness is Security:
Your admin password should be unique to Keycloak and not used for any other application. This minimizes the risk associated with password reuse.
4. Multiple-Factor Authentication (MFA):
Adding others factor of authentication significantly enhances your account's security. Such as :
- Application OTP
- SMS/e-mail OTP
- Magic Link
- WebAuthN device
- PassKeys
Remember, your admin account holds significant control over your Keycloak deployment, making its security paramount.
If you'd like more insights into password security best practices, check out our guide on Password Security Best Practices.
Take the necessary steps to fortify your admin account and enjoy a more secure Keycloak experience!
Penetration Test Report
Cloud-IAM do not provide a Penetration Test Report with supporting evidence for each dedicated Keycloak deployment we create for our customers. Consequently, we advise our customers to conduct their own audits of their deployments.
If you plan to conduct a penetration test, either internally or through an external company, we kindly request that you inform us in advance about the testing period and duration.